The Lord of the Rings: The Return of the King
The Lord of the Rings: The Return of the King is a 2003 epic high fantasy adventure film directed by Peter Jackson from a screenplay by Fran Walsh, Philippa Boyens, and Jackson. It is based on 1955's The Return of the King, the third volume of the novel The Lord of the Rings by J. R. R. Tolkien. The sequel to 2002's The Lord of the Rings: The Two Towers, the film is the third instalment in The Lord of the Rings trilogy. It features an ensemble cast including Elijah Wood, Ian McKellen, Liv Tyler, Viggo Mortensen, Sean Astin, Cate Blanchett, John Rhys-Davies, Bernard Hill, Billy Boyd, Dominic Monaghan, Orlando Bloom, Hugo Weaving, Miranda Otto, David Wenham, Karl Urban, John Noble, Andy Serkis, Ian Holm, and Sean Bean. Continuing the plot of the previous film, Frodo, Sam and Gollum make their final way toward Mount Doom to destroy the One Ring, unaware of Gollum's true intentions, while Merry, Pippin, Gandalf, Aragorn, Legolas, Gimli and their allies join forces against Sauron and his legions from Mordor.

Theatrical release poster
Statue of Sauron from The Lord of the Rings movies
The city of Minas Tirith was built from parts of the set of Helm's Deep, while the wide shots were from miniatures.
Epic films have large scale, sweeping scope, and spectacle. The term is slightly ambiguous, sometimes designating a film genre and at other times simply big-budget films. Like epics in the classical literary sense, it is often focused on a heroic character. An epic's ambitious nature helps to set it apart from other genres such as the period piece or adventure film.
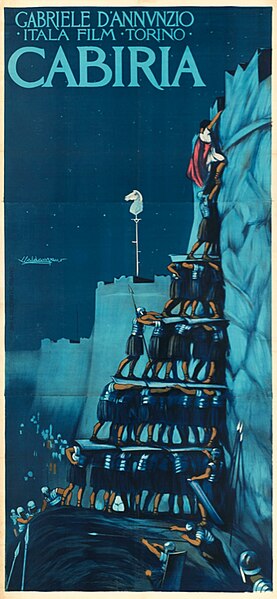
Italian film Cabiria (1914), one of the earliest known epic films