Quantum computing
Videos
Photos
A quantum computer is a computer that takes advantage of quantum mechanical phenomena. On small scales, physical matter exhibits properties of both particles and waves, and quantum computing leverages this behavior, specifically quantum superposition and entanglement, using specialized hardware that supports the preparation and manipulation of quantum states.

Quantum System One, a quantum computer by IBM from 2019 with 20 superconducting qubits

A wafer of adiabatic quantum computers
Quantum mechanics
Videos
Photos
Quantum mechanics is a fundamental theory in physics that describes the behavior of nature at and below the scale of atoms. It is the foundation of all quantum physics, which includes quantum chemistry, quantum field theory, quantum technology, and quantum information science.
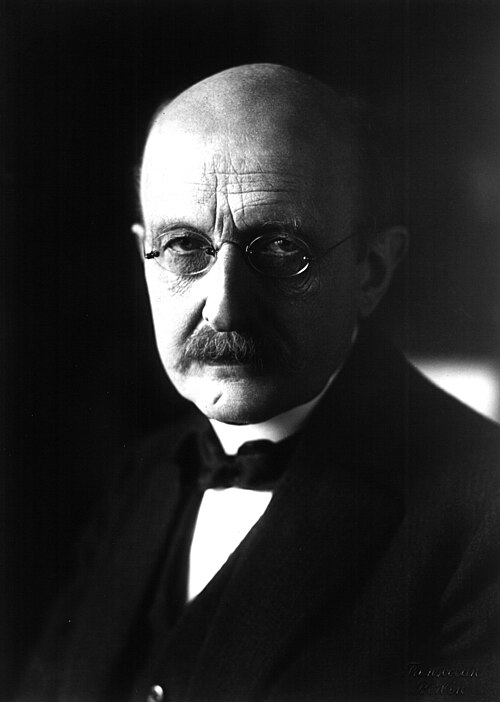
Max Planck is considered the father of the quantum theory.

The 1927 Solvay Conference in Brussels was the fifth world physics conference.