In cryptography, a brute-force attack consists of an attacker submitting many passwords or passphrases with the hope of eventually guessing correctly. The attacker systematically checks all possible passwords and passphrases until the correct one is found. Alternatively, the attacker can attempt to guess the key which is typically created from the password using a key derivation function. This is known as an exhaustive key search. This approach doesn't depend on intellectual tactics; rather, it relies on making several attempts.
The Electronic Frontier Foundation's US$250,000 DES cracking machine contained over 1,800 custom chips and could brute-force a DES key in a matter of days. The photograph shows a DES Cracker circuit board fitted with 64 Deep Crack chips using both sides.
Modern GPUs are well-suited to the repetitive tasks associated with hardware-based password cracking.
A single COPACOBANA board boasting 6 Xilinx Spartans – a cluster is made up of 20 of these
Cryptography, or cryptology, is the practice and study of techniques for secure communication in the presence of adversarial behavior. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, information security, electrical engineering, digital signal processing, physics, and others. Core concepts related to information security are also central to cryptography. Practical applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications.
Lorenz cipher machine, used in World War II to encrypt communications of the German High Command
16th-century book-shaped French cipher machine, with arms of Henri II of France
Enciphered letter from Gabriel de Luetz d'Aramon, French Ambassador to the Ottoman Empire, after 1546, with partial decipherment
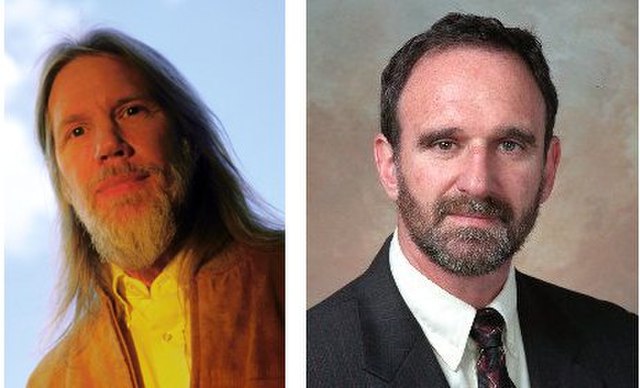
Whitfield Diffie and Martin Hellman, authors of the first published paper on public-key cryptography.