The Chaos Computer Club (CCC) is Europe's largest association of hackers with 7,700 registered members. Founded in 1981, the association is incorporated as an eingetragener Verein in Germany, with local chapters in various cities in Germany and the surrounding countries, particularly where there are German-speaking communities.
Since 1985, some chapters in Switzerland have organized an independent sister association called the Chaos Computer Club Schweiz (CCC-CH) instead.
Chaos Communication Camp 2003 near Berlin, featuring the Pesthörnchen [de] aka Datenpirat, a Jolly Roger malapropism to the logo of the former Deutsche Bundespost, the Federal Post of Germany
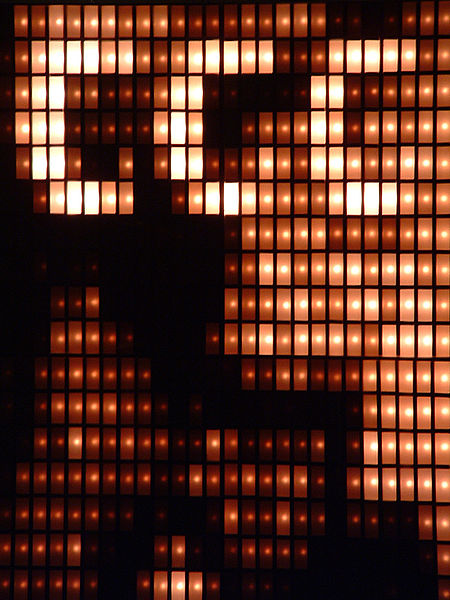
Blinkenlights at the 22nd Chaos Communication Congress
Mascot used to protest against the Staatstrojaner, a trojan horse
Chaos Communication Congress
The Chaos Communication Congress is an annual conference organized by the Chaos Computer Club. The congress features a variety of lectures and workshops on technical and political issues related to security, cryptography, privacy and online freedom of speech. It has taken place regularly at the end of the year since 1984, with the current date and duration established in 2005. It is considered one of the largest events of its kind, alongside DEF CON in Las Vegas.
Chaos Communication Congress
31C3 in Hamburg
Audience at the keynote of Glenn Greenwald at 30C3
The 22C3 in December 2005

![Chaos Communication Camp 2003 near Berlin, featuring the Pesthörnchen [de] aka Datenpirat, a Jolly Roger malapropism to the logo of the former Deutsch](https://upload.wikimedia.org/wikipedia/commons/thumb/a/a2/Ccc2003PirateTent.jpg/640px-Ccc2003PirateTent.jpg)