The World Trade Center site, often referred to as "Ground Zero" or "the Pile" immediately after the September 11 attacks, is a 14.6-acre (5.9 ha) area in Lower Manhattan in New York City. The site is bounded by Vesey Street to the north, the West Side Highway to the west, Liberty Street to the south, and Church Street to the east. The Port Authority of New York and New Jersey (PANYNJ) owns the site's land. The original World Trade Center complex stood on the site until it was destroyed in the September 11 attacks.
The original Twin Towers of the World Trade Center in 1992
The site as it appeared twelve days after 9/11
Berenice Abbott's photograph showing Radio Row in 1936, with Cortlandt Street station seen in the background
The original World Trade Center complex
A hypocenter or hypocentre, also called ground zero or surface zero, is the point on the Earth's surface directly below a nuclear explosion, meteor air burst, or other mid-air explosion. In seismology, a hypocenter of an earthquake is its point of origin below ground; a synonym is the focus of an earthquake.
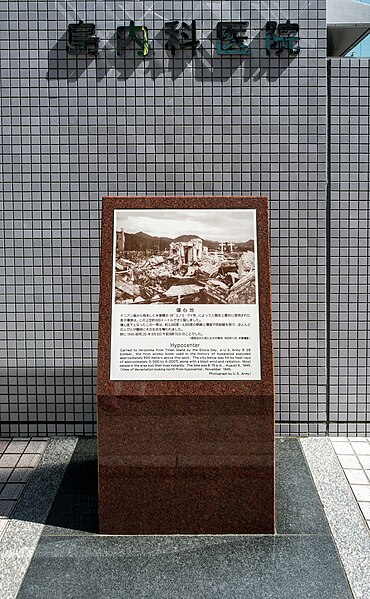
Monument marking the hypocenter, or ground zero, of the atomic bomb explosion over Hiroshima.
The former hot dog stand nicknamed Cafe Ground Zero in the Pentagon's center courtyard.
Aerial view of the World Trade Center site in September 2001.